Security Principles for Hackers
In this tutorial, we're going to dive into the core principles of security that every hacker needs to understand. Before you can effectively break security, you need to know how security is built. Consider this your foundation for everything we'll do in the future.
What is "Security"?
Security has become just another marketing buzzword these days. Every company wants to claim their product is "secure."
But here’s the truth: perfect security doesn’t exist. No system is 100% secure—there’s always a way in. A hacker’s job is to find it, while a defender’s job is to make that as difficult as possible.
Know Your Enemy (and Yourself)
Before we dive into technical security concepts, you need to understand the first principle of security: know who you're up against.
Are you trying to keep out a curious toddler from accessing your laptop? Or are you protecting valuable technical designs worth millions from corporate spies? These are entirely different scenarios requiring different approaches.
As a hacker, this works both ways – you need to understand who you're targeting and
what defenses they're likely to have in place. This is how you begin planning your attack
strategy.
Step #1: The CIA Triad
When security professionals evaluate a system, they look at three core principles known as the CIA triad:
1. Confidentiality – Is the secret stuff staying secret?
2. Integrity – Is the data being protected from unauthorized changes?
3. Availability – Can legitimate users access the system when needed?

Let's break these down with a real-world example that everyone understands: online banking.
Confidentiality
When you log into your bank account, you expect your financial information to stay private. If someone can spy on your transactions or steal your credentials, that's a confidentiality breach.
Integrity
Imagine transferring $100 to a friend, but a hacker intercepts and changes the recipient to their own account. That's an integrity breach.
Availability
If you need to make an urgent payment but the bank's website is down, that's an availability failure.
Step #2: The DAD Triad
The security of a system is attacked through one of several means. It can be via the disclosure of secret data, alteration of data, or destruction of data.
- Disclosure is the opposite of confidentiality. In other words, disclosure of confidential data would be an attack on confidentiality.
- Alteration is the opposite of Integrity. For example, the integrity of a cheque is indispensable.
- Destruction/Denial is the opposite of Availability.

Let's see how this works in another real-world scenario: healthcare systems.
Disclosure Attacks on Healthcare Data
Healthcare records contain everything from social security numbers to medical conditions – information that's both sensitive and valuable. Hackers target these systems to steal patient data.
Alteration of Medical Records
Imagine changing someone's blood type or medication allergies in their electronic health record. For a targeted attack, this could literally be life-threatening.
Destruction/Denial in Hospital Systems
Ransomware attacks on hospitals have become increasingly common. By encrypting critical systems, attackers can literally put lives at risk and demand payment to restore service.
Step #3: Security Models
To understand how to break systems, you need to understand how they're designed to be secure. Let's look at three fundamental security models:
Bell-LaPadula Model: Military-Grade Confidentiality
This model comes from the military and focuses on keeping secrets secret with two main rules:
- No Read Up – You can't read information classified above your clearance level.
- No Write Down – You can't write information to a lower classification level where more people could see it.
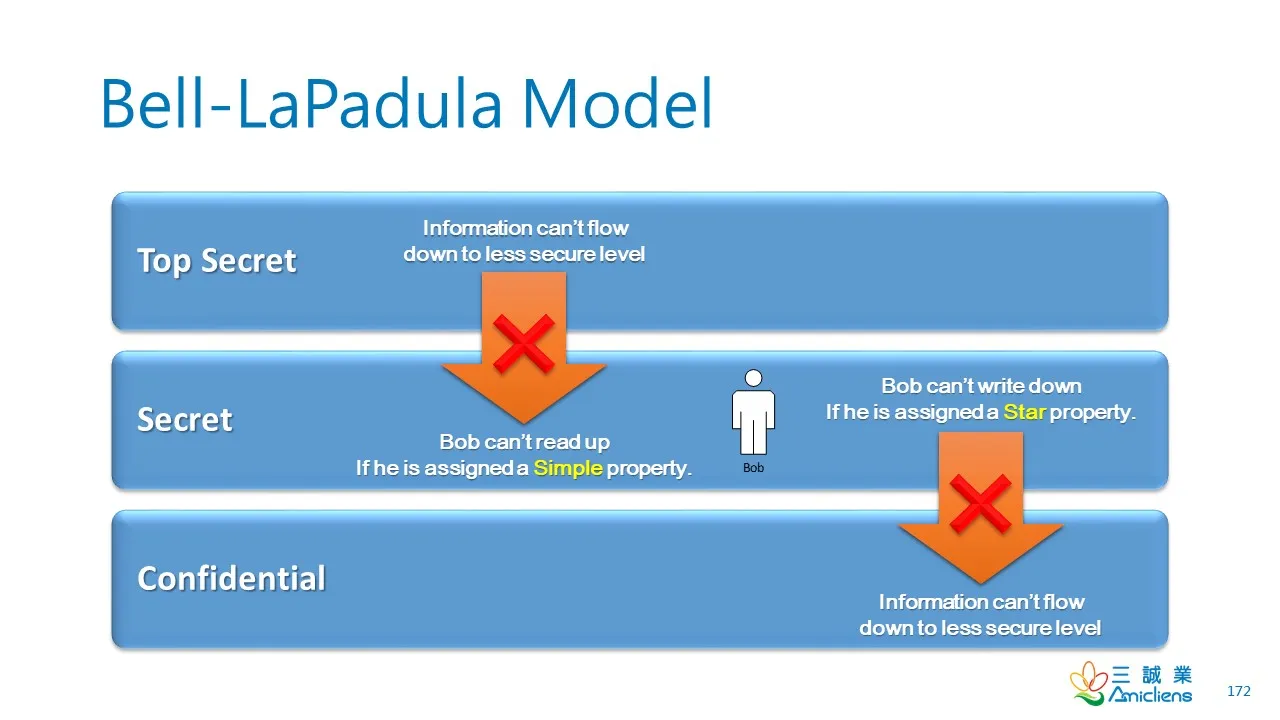
The shorthand is "write up, read down."
Finding ways around Bell-LaPadula is the foundation of privileges escalation attacks.
Biba Model: Keeping Your Data Clean
The Biba model is all about integrity and works almost exactly opposite to Bell-LaPadula:
- No Read Down – Don't read data from less trusted sources that might corrupt your system.
- No Write Up – Don't write data to higher integrity systems that require pristine information.
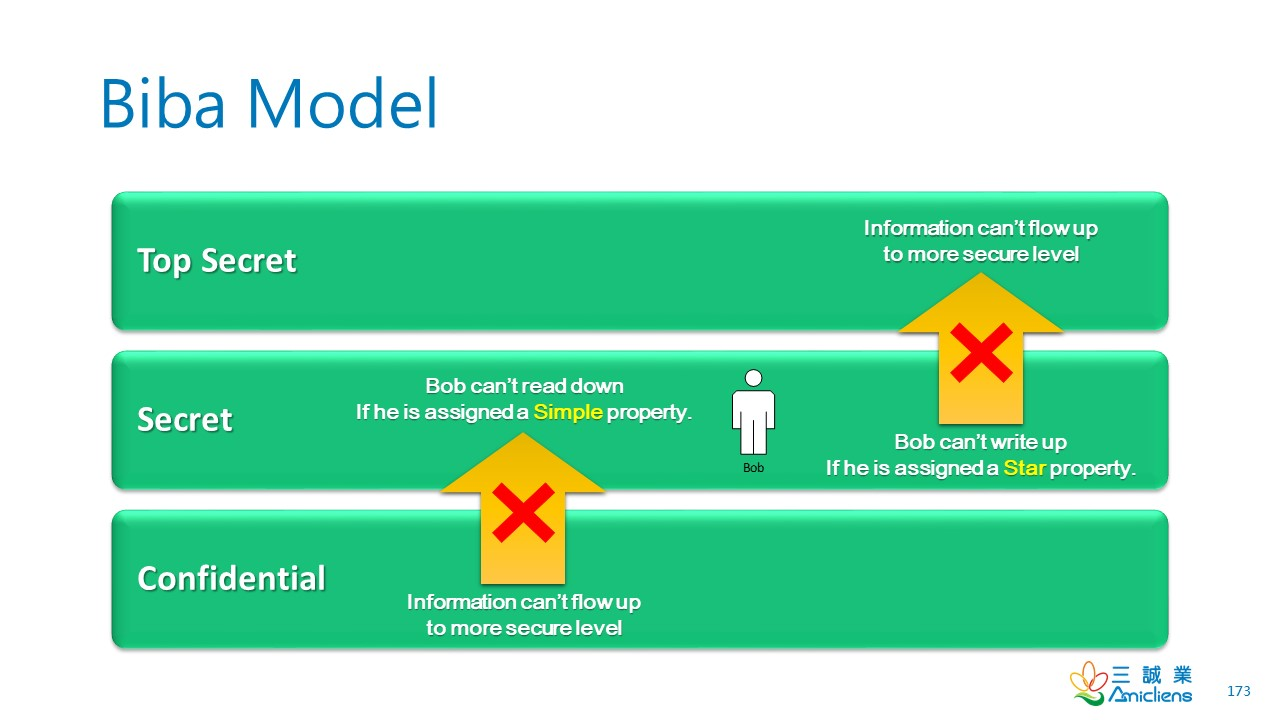
This one follows "read up, write down."
Data poisoning attacks specifically target weaknesses in Biba-style implementations.
Clark-Wilson Model: Following the Money
The Clark-Wilson model was designed for commercial applications like banking. It categorizes data and controls how it can be accessed and modified:
- Constrained Data Items (CDIs) – The important stuff that needs protection.
- Unconstrained Data Items (UDIs) – Everything else, like user input.
- Transformation Procedures (TPs) – The only way to change important data.
- Integrity Verification Procedures (IVPs) – Checks that data hasn't been tampered with.
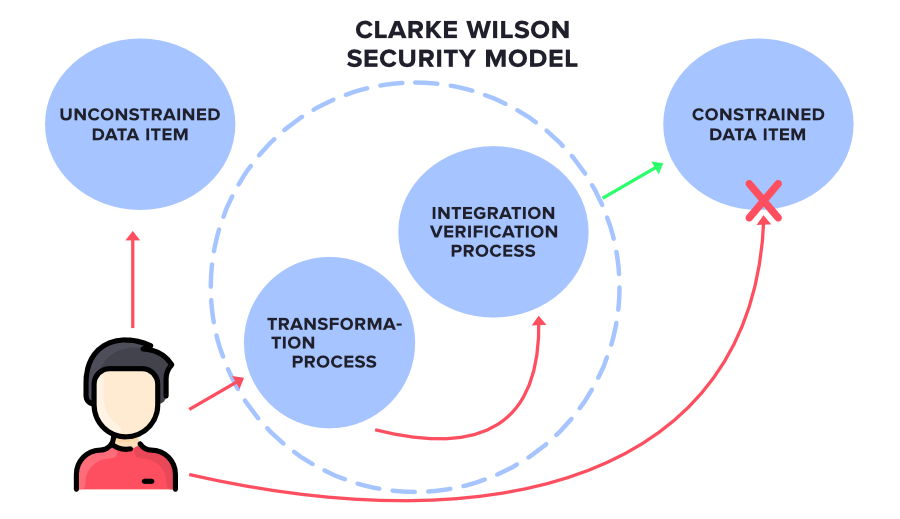
Finding ways to bypass transformation procedures or corrupt verification systems is how hackers attack Clark-Wilson systems.
Balancing Act: The Security Trade-Off
The more you strengthen one area of security, the more you typically weaken another.
- Increase encryption for better confidentiality? You might slow down the system, affecting availability.
- Add more verification steps for integrity? Users get annoyed and might create workarounds, reducing confidentiality.
Conclusion
Security isn't a feature or a product – it's a continuous process of balancing competing priorities against real-world threats. By understanding these fundamental principles, you're now better equipped to think like both a defender and an attacker.
This is just the beginning of your journey, my hacker apprentices. Keep learning, stay curious, and remember – with great power comes great responsibility.